May 4, 2026
Digital Trust without Surrender or Surveillance
Our years of experience in supporting privacy for money and communication offers a new solution for digital trust
For Fedi, community is not just a feature of the app. It is best thought of as the underlying technology. Existing long before the internet, we see community as humanity’s oldest and most durable system for coordination, resilience, and, above all, trust.
The challenge is to translate community trust into a form that can be attached to an individual’s online life while maintaining privacy.
We are exploring whether the privacy-preserving features of the Fedimint protocol can extend beyond bitcoin-backed eCash to trust and reputation. This is in service of building a trust framework that works with Fedi’s values and that utilises Fedi’s greatest asset: our global community network.
F2F: The Best P2P Technology
Over the past few years, Fedi has built an on-the-ground network of trusted participants across global Bitcoin communities. This includes Fedi Masters (our regional leaders) and the Fedi Knights who support them.
These are people with real community credibility. They show up in person, run workshops, answer questions, and build trust face-to-face (or “F2F”). Many are known less as Fedi representatives than as peers who have earned trust over time. They locate and support a growing network of local Community Leaders who have a similar standing within their communities.
These two groups have cultivated community trust within the Fedi ecosystem. As such, they can serve as the root of a trust system capable of 1) conferring proof-of-human credentials, 2) attesting to that person’s trustworthiness, and, eventually, 3) enabling others to do the same — all while preserving privacy. It also provides a template that other communities can model themselves after.
How It Starts
The process starts in person and seeks to verify two things:
Self-evidently, “Is this person an individual?”
Less obvious, “At what level is this person trustworthy?”
Upon meeting, an authorised Verifier (e.g., a Fedi Master or Community Leader) confirms that the User is a unique individual.
Before signing, the Verifier can select a key that attaches a specific level of trustworthiness to the User based on a simple, publicly available scoring system. That score serves as a rough indication for the User’s trustworthiness.
If the score reaches a certain target, the Verifier then signs a blinded public key that the User provides, such as a Nostr nPub. Once that signature is unblinded, the User holds a verified credential without exposing their real-world identity. As the Verifier provides attestations for multiple individuals, the User can also be assured that their anonymity will be maintained — one person obscured among a crowd of many.
Result: The User now holds a signed credential from a trusted Verifier that attests to their uniqueness and trustworthiness.
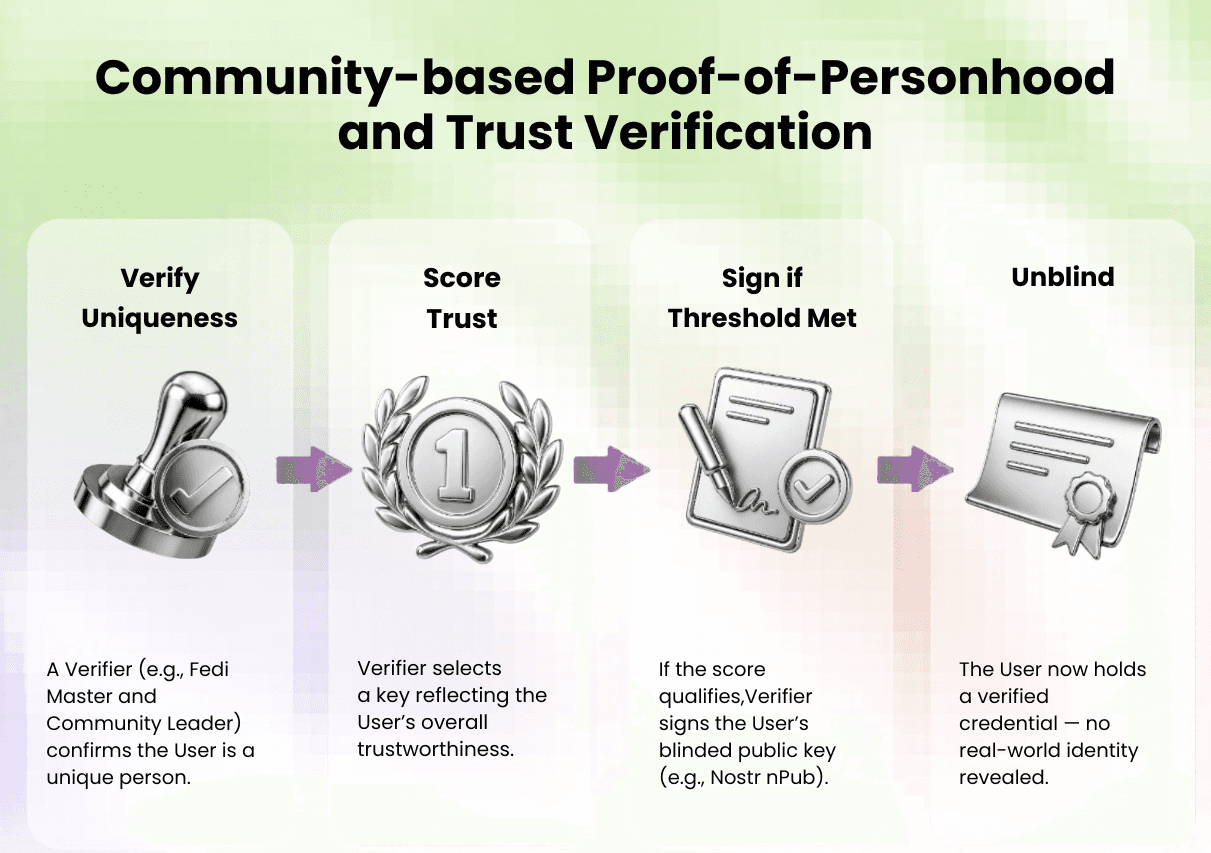
Fig. 1: The verification process.
No database. No digital breadcrumbs. No system that demands you give up your privacy.
This could be deployed immediately on a Nostr-powered service like Primal, offering something akin to Twitter/X’s original blue checkmark from when it signalled earned credibility rather than a purchasable badge. The key differences:
the attestation carries an added layer of community-verified trust; and
privacy is preserved by a decentralised group rather than a technology company.
Along the evolution to an open protocol, this system can expand beyond its Fedi origins, where communities can apply their own authority structures. Verifiers can also choose to provide this as a free service or for a small fee.
Trust is Best When Slow-but-Sure
While they approach the topic of trust to varying degrees, a lot of digital identity projects start from the assumption that the only way to prove you’re human is:
collect something deeply personal; and/or
store or otherwise handle that data where the information can be stolen, hacked, or misused.
On the other hand, the Fedi approach relies on real-world interaction (i.e., the way trust in communities has always worked) and the individual can observe that no personally identifiable information is asked for, taken, or retained. Further, if abused, the Fedi credential is easily revocable.
We recognise and accept that our proposed approach doesn’t scale rapidly. After all, interactions in the world of matter and substance move a lot slower than that of digits and data. We’re prioritising the use of well-established, “real world” networks over speed in order to jointly support two core benefits over the long term: trust and decentralisation.
Mitigating Abuse
The system can limit abuse by placing caps on how many verifications each Verifier can issue within a given period, while keeping those caps high enough to protect user privacy.
Verifiers can preserve the integrity of their verifications by limiting such service to people within their geography. This ensures that verifications will be more carefully conferred to a User that they are more likely to know well.
This approach won’t stop all attacks, but it prevents them from spreading or causing large-scale damage.
A New Trust System: Private and Participatory
As stated at the outset, community is the most well-tested foundational technology for trust — it just needs better tools for rebalancing towards privacy in the AI age. We strongly believe that a community-based attestation system, handled right, can be both private and participatory.
This offers an alternative to less-than-ideal systems too often built on biometric data, permanent public trails, or invasive disclosure — made especially critical in an era of ever increasing threats to physical safety, such as “wrench attacks.”
Just as important, this cannot remain a closed centralised system. To work at all, it must become an open, privacy-preserving trust protocol that grows well beyond its Fedi origins. Different communities will have different structures, norms, and trust relationships. The goal is to give them a shared, privacy-preserving framework for conferring, recognising, and revoking attestations.
